LISTEN TO STORY
WATCH STORY
By: Pramod Chinthaka Peiris
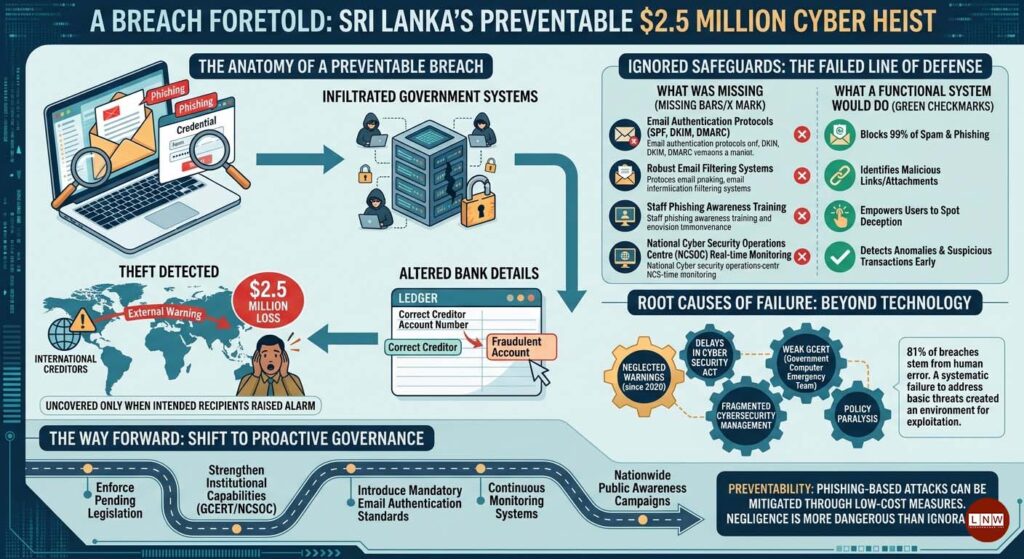
April 29, Colombo (LNW): Sri Lanka’s largest-ever state cyber theft, amounting to a staggering $2.5 million, has exposed a profound failure in governance, not merely of technology but of foresight. The breach, which targeted the Finance Ministry in early 2026, was not the result of an unforeseeable cyber onslaught. Instead, it was the culmination of neglected warnings, ignored safeguards, and a systemic failure to address one of the most basic and preventable threats in the digital age: spam-driven phishing attacks.
At its core, the incident illustrates the dangerous intersection between hacking and spamming—two distinct yet increasingly interconnected cyber threats. While hacking involves the exploitation of system vulnerabilities to gain unauthorised access, spamming relies on mass unsolicited communication, often as a vehicle for deception. In this case, the latter appears to have served as the gateway for the former.
The Anatomy of a Preventable Breach
The attack unfolded when hackers infiltrated government systems and altered bank details linked to sovereign debt repayments intended for international creditors, including Australia and potentially India. The manipulation went undetected until the intended recipients themselves raised the alarm. By then, millions had already been siphoned away.
What makes this breach particularly alarming is not merely its scale, but its simplicity. Evidence strongly suggests that the attackers gained initial access through phishing emails—messages designed to appear legitimate while tricking recipients into divulging credentials or executing malicious instructions. Such methods do not require sophisticated exploits; rather, they prey on predictable human behaviour and weak institutional safeguards.
Globally, phishing remains one of the most successful cyberattack vectors, with studies indicating that approximately 81% of breaches stem from human error, often triggered by deceptive emails. In Sri Lanka’s case, this pattern appears to have repeated itself with costly consequences.

A Failure to Address the Obvious
Perhaps the most damning aspect of the incident is the government’s failure to implement well-established anti-spam measures. Modern cybersecurity frameworks emphasise preventative tools such as email authentication protocols—SPF, DKIM, and DMARC—which can block up to 99% of spam and phishing attempts when properly deployed. These are not cutting-edge innovations but standard practices in even moderately secure systems.
Yet, Sri Lankan authorities appear to have overlooked these basic defences. There was no evidence of robust email filtering systems, no comprehensive staff training programmes to identify phishing attempts, and no sustained public awareness campaigns. The absence of these measures created an environment in which malicious emails could circulate freely, eventually enabling unauthorised access to critical financial systems.
Compounding this failure was the lack of real-time monitoring. A functioning National Cyber Security Operations Centre (NCSOC), operating with continuous oversight, could have detected anomalies in financial transactions or suspicious system activity at an early stage. Instead, the breach remained undetected until external parties intervened.
Structural Weaknesses and Policy Paralysis
The breach did not occur in a vacuum. Since as early as 2020, proposals for a comprehensive Cyber Security Act and the strengthening of the Government Computer Emergency Readiness Team (GCERT) had been under discussion. However, implementation delays meant that these frameworks remained largely theoretical at the time of the attack.
This policy inertia proved costly. Without enforceable standards or coordinated oversight, government institutions were left to manage cybersecurity risks in a fragmented and inconsistent manner. Basic practices—such as timely software updates, secure configurations, and multi-factor authentication—were either inadequately applied or entirely absent.
The situation is further exacerbated by Sri Lanka’s ongoing digital transformation initiatives, including programmes aimed at modernising public services. While these efforts are essential for economic recovery and efficiency, they also expand the attack surface. Without corresponding investments in cybersecurity—particularly in areas as fundamental as spam prevention—such initiatives risk becoming liabilities rather than assets.
Lessons Ignored, Consequences Paid
The tragedy of this breach lies in its preventability. Unlike sophisticated zero-day exploits or highly targeted cyber-espionage campaigns, phishing-based attacks can be effectively mitigated through relatively low-cost measures. Spam filters, authentication protocols, and user awareness training form the first line of defence, often stopping malicious communications before they reach their targets.
Had these measures been properly implemented, the outcome could have been markedly different. Phishing emails might have been blocked at the gateway, suspicious links flagged, and fraudulent instructions identified before any financial damage occurred.
Instead, the government’s failure to act on known vulnerabilities allowed a preventable threat to escalate into a national financial crisis. The incident serves as a stark reminder that in cybersecurity, negligence is often more dangerous than ignorance.
What Happens Next?
To prevent a recurrence, Sri Lanka must urgently shift from reactive to proactive cybersecurity governance. This includes enforcing pending legislation, strengthening institutional capabilities, and prioritising basic yet highly effective measures such as spam prevention and user education.
The introduction of mandatory email authentication standards, continuous monitoring systems, and nationwide awareness campaigns could significantly reduce the risk of similar attacks. Equally important is the need for accountability—ensuring that failures of this magnitude are thoroughly investigated and addressed at both technical and administrative levels.
In the final analysis, the $2.5 million loss is not merely a financial setback but a warning. It underscores the cost of complacency in an era where the most dangerous threats are often the simplest to prevent.

